Enhance Your Internet Security with ISO 27032 Guidelines

ISO 27032 Guidelines: Practical Steps to Strengthen Internet Security
ISO 27032 is a voluntary international guidance focused on internet security and the collaborative side of cybersecurity across organizations and networks. This article walks through how ISO 27032 frames cyber risk management, incident handling, and protection for critical information infrastructure so you can strengthen your overall security program. You’ll learn what ISO 27032 covers, how it complements ISO 27001 and an ISMS, a practical implementation roadmap, measurable benefits, and which teams should prioritise adoption. The guidance is action-oriented: it maps core domains, recommends risk-based priorities, and prescribes governance and monitoring that reduce exposure to phishing, data breaches, and disruptive attacks. Later, we explain how AI-driven auditing speeds gap analysis, enables continuous monitoring, and supports certificate management via a partner like Stratlane Certification. Follow this structured path to align technical controls, governance and incident response with modern internet-scale threats and fold ISO 27032 principles into your ISMS and compliance programs.
What is ISO 27032 and How Does It Guide Cybersecurity?
ISO 27032 provides guidance to improve cybersecurity by focusing on internet security, cross-network coordination, and protection of critical information infrastructure. It clarifies roles between stakeholders, defines responsibilities during incidents, and recommends cross-organizational controls that augment existing information security standards. Because it’s guidance-based—not a certifiable standard—organizations adopt its practices to enhance frameworks like ISO 27001 and harmonise cyber risk management across partners and suppliers. The net effect is clearer coordination between technical controls, governance and external parties, which reduces both the likelihood and impact of cyber incidents. Understanding ISO 27032’s scope and core domains helps teams map controls and identify integration points with their ISMS and operational processes.
- Core domains covered by ISO 27032:
Internet Security: Protecting services and applications exposed to public networks.
Network Security: Secure connectivity, segmentation, and resilience planning.
Information Security: Protecting confidentiality, integrity, and availability of data.
Critical Information Infrastructure Protection (CIIP): Securing essential services and their dependencies.
These domains translate into a mix of policy, process and technical controls that organizations can tailor to their risk profile and ecosystem dependencies. The following section dives deeper into each domain with practical control examples.
What Are the Core Domains of ISO 27032 Guidelines?
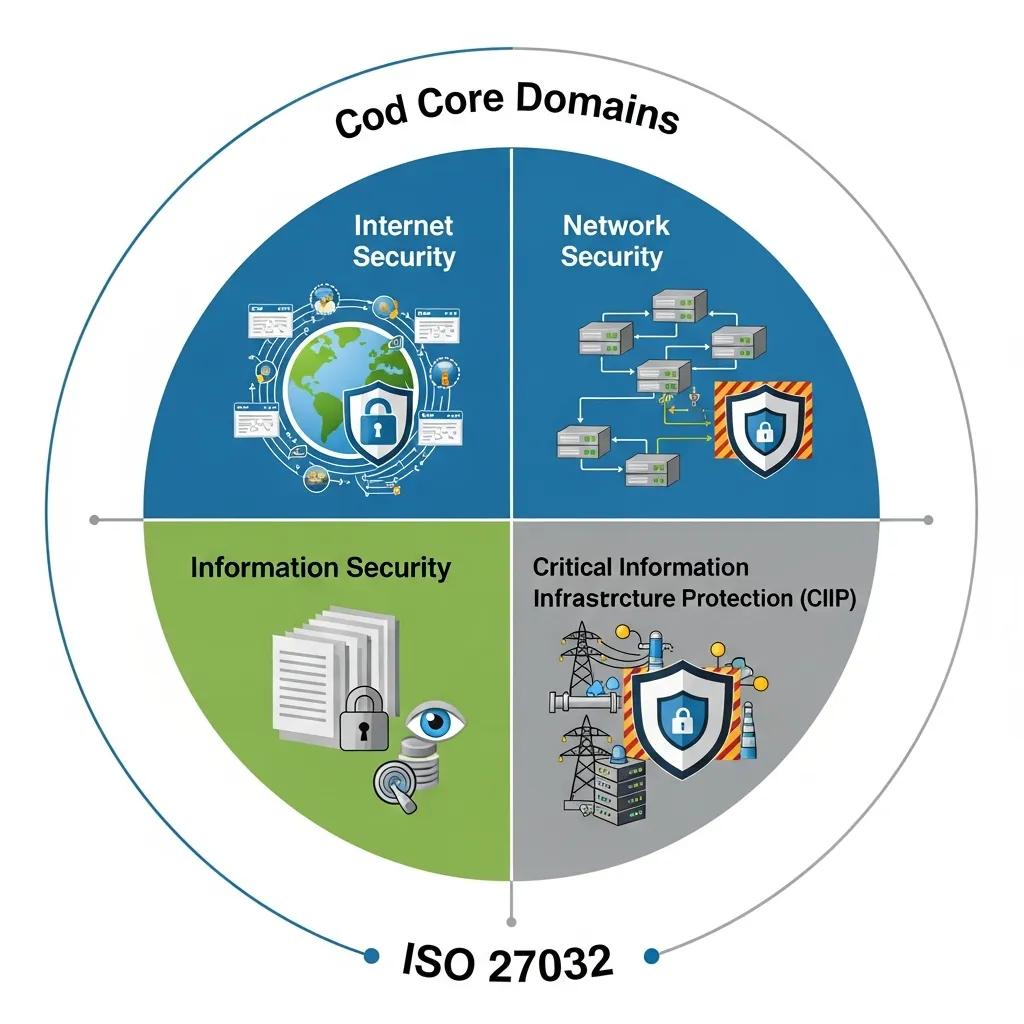
ISO 27032 groups its focus into four domains—internet security, network security, information security and CIIP—each addressing different threats and mitigations. Internet security emphasises secure application design, web gateway controls, DNS hardening and secure APIs to limit exposure to the public internet. Network security targets segmentation, secure remote access and resilience planning to reduce lateral movement and preserve connectivity during incidents. Information security aligns with confidentiality, integrity and availability controls—encryption, access management and reliable backups—to protect data at rest and in transit. CIIP covers systemic dependencies for critical services, recommending redundancy, supplier resilience and coordinated incident response across stakeholders. Together, these domains form an integrated approach teams can map to specific controls that underpin a coordinated cyber risk program.
How Does ISO 27032 Complement ISO 27001 for Cybersecurity Frameworks?
ISO 27032 extends an ISMS by focusing on cyber-specific coordination, stakeholder relationships and internet-scale risks that sit outside internal information security processes. ISO 27001 defines the ISMS lifecycle—risk assessment, control selection and continuous improvement—while ISO 27032 fills gaps around cross-organizational incident response, threat intelligence sharing and CIIP dependencies. Practically, organizations map ISO 27032 recommendations to ISMS clauses and controls to prioritise cyber threats and operationalise external communication channels. For teams already certified to ISO 27001, adopting ISO 27032 guidance strengthens resilience without adding duplicate certification steps, and it clarifies procedures for collaborative incident handling and partner coordination. The next section lays out a step-by-step implementation roadmap to realise these synergies.
Research also shows how combining ISO 27032 and ISO 27001 creates a stronger framework for cloud cybersecurity risk management.
ISO 27032 & 27001 for Cloud Cybersecurity Risk Management
A literature review and framework proposal that compares cloud computing security concerns across ISO and NIST standards, then outlines a combined approach using ISO 27032, ISO 27001, ISO 27017 and the NIST Cybersecurity Framework for managing cloud-related cyber risks.
Cybersecurity management in cloud computing: semantic literature review and conceptual framework proposal, S El Kafhali, 2021
| Guideline Component | Characteristic | Primary Focus |
|---|---|---|
| Internet Security | Application and service hardening | Reduce external attack surface |
| Network Security | Segmentation and secure access | Limit lateral movement and improve resilience |
| Information Security | Data protection measures | Ensure CIA: confidentiality, integrity, availability |
| CIIP | System-level resilience and coordination | Protect essential services and dependencies |
How to Implement ISO 27032 Guidelines Effectively?
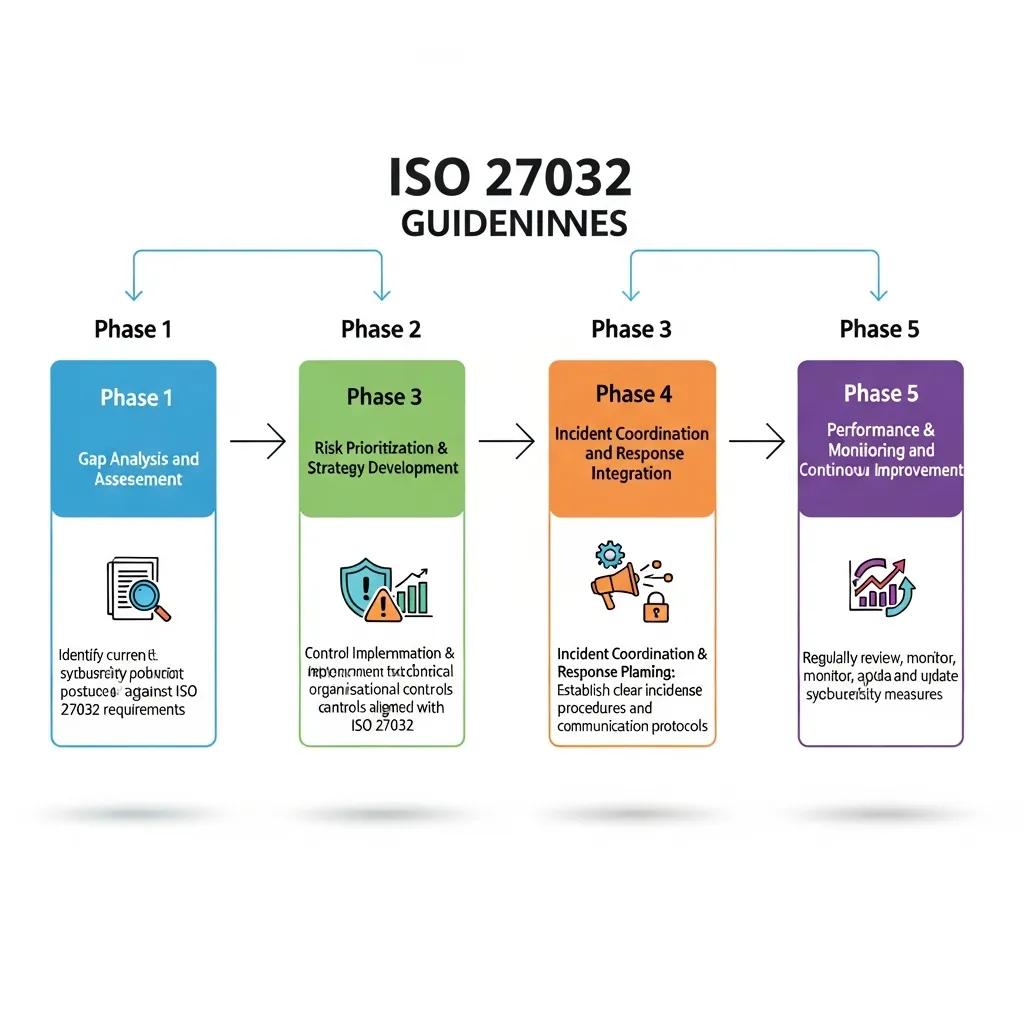
Effective ISO 27032 adoption follows a structured roadmap: align guidance to your ISMS, prioritise risks, and embed incident coordination plus continuous monitoring into daily operations. Treat ISO 27032 as a layer on top of the ISMS: run a cyber-focused gap analysis, target controls that reduce high-impact internet-facing risks, and define governance for multi-party incident response. Implementation delivers better cross-domain visibility, clearer escalation paths and pragmatic control choices that match your threat landscape. Below we break the process into concrete steps and a governance checklist to operationalise ISO 27032 recommendations.
To achieve measurable outcomes, follow these essential steps for ISO 27032 alignment:
- Conduct a cyber-focused gap analysis mapping internet-facing assets and third-party dependencies.
- Prioritise controls with a risk matrix that accounts for threat likelihood, exposure and impact on critical services.
- Define incident coordination roles, communication channels and escalation criteria with external stakeholders.
- Integrate continuous monitoring and threat intelligence into the ISMS improvement cycle.
- Validate controls through testing, tabletop exercises and periodic reassessment.
These steps create a repeatable implementation pathway that ties strategy to operational controls and continuous improvement. The next subsection outlines the core risk management cycle in more detail.
What Are the Key Steps in Cyber Risk Management Under ISO 27032?
Risk management under ISO 27032 starts by identifying internet-exposed assets and modelling threats across stakeholder boundaries, then moves through assessment, mitigation and monitoring in a continuous loop. Identification relies on asset inventories, network maps and dependency analysis to expose attack paths and single points of failure. Assessment quantifies risk with likelihood and impact metrics, often enriched with threat intelligence for scenarios like phishing, malware or DDoS. Mitigation uses layered technical, administrative and contractual controls focused on high-risk assets and CIIP dependencies. Monitoring employs telemetry, anomaly detection and regular testing to validate control effectiveness. Lessons learned feed back into the ISMS and governance processes so evolving threats are managed proactively.
How to Develop Cybersecurity Policies and Governance Aligned with ISO 27032?
Translating ISO 27032 into policy and governance means assigning clear roles, setting measurable KPIs, and formalising coordination mechanisms with partners and suppliers. Start by scoping what internet services, third-party interfaces and CIIP elements are covered, then assign ownership for detection, response coordination and external communications. Use a RACI model for cross-organizational tasks and track KPIs such as mean time to detect (MTTD), mean time to respond (MTTR), and percentage of critical dependencies with resilience plans. Training and tabletop exercises make procedures real—ensuring teams and partners know escalation steps and communication templates. Strong governance enables coordinated responses and continuous improvement of cybersecurity posture.
- Governance checklist:
Assign clear ownership for cross-stakeholder incident coordination.Define escalation thresholds and external notification procedures.Establish KPIs and a reporting cadence for cyber resilience metrics.
This governance foundation readies organizations to realise the benefits of ISO 27032 alignment described below.
What Are the Benefits of Aligning with ISO 27032 Guidelines?
Adopting ISO 27032 delivers measurable benefits: reduced incident impact, faster coordinated response, stronger supply-chain trust, and an improved regulatory stance where internet security expectations apply. Its focus on cross-stakeholder coordination and CIIP resilience shortens containment times and shrinks systemic attack surfaces across partner ecosystems. Teams commonly see better detection rates and clearer recovery playbooks after implementing structured governance and prioritized technical controls. Beyond operational improvements, demonstrating alignment with recognized cyber guidance supports procurement confidence and customer trust—especially when digital services are critical to business operations. The table below maps these outcomes to tangible impacts.
| Benefit | Metric / Example | Business Impact |
|---|---|---|
| Reduced incident impact | Shorter MTTR by up to 30% (example target) | Lower downtime costs and reputation damage |
| Faster coordinated response | Faster cross-stakeholder escalation | Quicker containment of multi-party incidents |
| Improved regulatory alignment | Clearer evidence of cyber governance | Easier procurement and contractual compliance |
| Increased resilience | Redundancy and CIIP plans | Continuity for critical services and revenue protection |
How Does ISO 27032 Enhance Cybersecurity Posture and Data Protection?
ISO 27032 strengthens posture by formalising controls that reduce exposure of internet-facing assets and by integrating detection and response across organizational boundaries. Technical measures—segmentation, multi-factor authentication, secure APIs and comprehensive logging—shrink attack surfaces and improve forensic visibility. Process changes—centralised incident coordination, threat intelligence sharing and supplier resilience plans—speed containment and recovery. Expected outcomes include reduced dwell time, better patch and configuration hygiene, and clear evidence trails for post-incident analysis. Together these changes improve data protection, lower breach likelihood, and help meet sector expectations for secure service delivery.
What Role Does ISO 27032 Play in Regulatory Compliance and Trust Building?
ISO 27032 supports regulatory alignment by providing structured guidance for internet security practices that match many regulator expectations for risk-based controls and incident readiness. While not certifiable, ISO 27032 maps to compliance requirements like breach notification, supply-chain risk management and continuity planning. Adopting its practices signals to customers and partners that your organization has coordinated protection mechanisms for internet and infrastructure dependencies—an advantage in procurement and trust-building. Pairing ISO 27032 guidance with ISO 27001 certification further demonstrates both operational controls and governance maturity.
- Compliance & trust actions:
Map ISO 27032 outcomes to regulatory artifact requirements.
Use incident coordination procedures to meet notification timelines.
Provide stakeholders with evidence of supplier resilience and testing.
Many teams choose an assessment partner to speed adoption and maintain continuous assurance. The section below explains how Stratlane’s AI-driven auditing supports those goals.
How Does Stratlane's AI-driven Auditing Support ISO 27032 Implementation?
Stratlane Certification combines AI-driven auditing tools with experienced auditors to accelerate ISO 27032 alignment. Our platform automates coverage mapping, spots gaps in internet-facing controls and enables continuous assessment. AI speeds discovery of exposed assets and correlates telemetry to guideline controls, while human auditors validate context and prioritise remediation. This hybrid approach shortens initial gap analysis, expands coverage beyond manual sampling, and supports certificate management for related standards like ISO 27001. The result is a practical, repeatable assessment cadence that plugs into your ISMS and keeps resilience on track. The following subsections outline AI capabilities for gap analysis and the benefits of continuous AI monitoring.
Before the table, a quick note: comparing traditional and AI-driven auditing helps organisations weigh trade-offs in speed, coverage, cost and continuous capability when choosing an audit approach.
| Audit Approach | Characteristic | Business Impact |
|---|---|---|
| Traditional Auditing | Periodic, manual sampling | Good for in-depth context but limited coverage and slower cycles |
| AI-driven Auditing | Automated discovery, pattern detection | Broader coverage, faster gap identification, cost-efficient repeatability |
| Hybrid (AI + Human) | AI identifies leads, humans validate | Best balance of scale, accuracy and context for remediation prioritisation |
How Does AI Enable Efficient Gap Analysis and Cybersecurity Assessments?
AI-based gap analysis uses automated asset discovery, pattern recognition in logs and mapping of findings to control frameworks to surface non-compliance or exposure quickly. Automation reduces manual inventory work and highlights anomalous configurations or unpatched services that traditional audits might miss between cycles. Pattern detection groups related findings and estimates potential impact, allowing teams to focus remediation on the highest risks. Human auditors then review AI-flagged evidence, apply contextual judgement and confirm priorities—creating a faster, repeatable assessment cycle that feeds actionable remediation roadmaps directly into ISMS processes.
What Are the Advantages of Continuous Monitoring and Improvement with AI?
Continuous AI monitoring delivers near-real-time detection of deviations from expected configurations and emerging threats, cutting detection latency and enabling proactive remediation. AI can prioritise alerts by likely impact and exploitability, supplying validated insights into the ISMS improvement cycle to guide control tuning. Regular automated assessments also build evidence trails that simplify re-assessment and certificate management for related standards. When combined with periodic human reviews, continuous monitoring ensures small issues are caught early and governance decisions remain informed by current operational risk data. The next section explains who should prioritise ISO 27032 adoption.
Who Should Implement ISO 27032 Guidelines and Why?
ISO 27032 is particularly valuable for organizations that operate internet-facing services, manage critical infrastructure dependencies, or coordinate across complex ecosystems where multi-party incidents can cascade. It benefits entities that need clear incident coordination, supplier resilience and stronger internet security posture. Sectors with high exposure—finance, healthcare, managed service providers, critical infrastructure operators and platform providers—see outsized value because of regulatory scrutiny and systemic risk. Small and medium enterprises that rely on cloud services or IoT can also benefit by applying risk-based priorities to secure external interfaces without overinvesting. Below are target audiences with concrete examples.
- Organisations that should prioritise ISO 27032:
Managed Service Providers: Secure multi-tenant services and coordinate incidents across clients.
Financial Institutions: Protect payment channels, APIs and regulatory reporting systems.
Healthcare Providers: Safeguard patient data and maintain continuity for critical care systems.
Critical Infrastructure Operators: Ensure resilience of essential services and supplier networks.
These examples show where cross-stakeholder coordination and CIIP-focused planning deliver the largest risk reduction. The next subsection maps ISO 27032 recommendations to common threats like phishing and data breaches.
Which Organizations Benefit Most from ISO 27032 Cybersecurity Framework?
Organizations with high internet exposure or complex supplier ecosystems benefit most because ISO 27032 emphasises coordination, incident response and CIIP resilience. Managed service providers benefit from standardised incident coordination across clients and suppliers, reducing containment time for cross-customer incidents. Financial firms gain clearer guidance on protecting APIs and payment channels plus evidence collection during incidents. Healthcare providers formalise supplier resilience and recovery plans to protect PHI and critical systems. Critical infrastructure operators need CIIP-focused redundancy and cross-stakeholder response playbooks to preserve public safety and continuity. These targeted adoptions translate into measurable business protection.
How Does ISO 27032 Address Specific Cyber Threats Like Phishing and Data Breaches?
ISO 27032 maps mitigations to common threats by combining technical controls, process changes and coordination practices that reduce attack success and speed recovery. For phishing, recommended measures include email authentication, user training, behavioural detection and clear escalation and containment procedures. For data breaches, the guideline stresses strong access controls, encryption, logging and coordinated evidence collection with partners and regulators. For DDoS and availability attacks, CIIP recommendations cover redundancy, traffic filtering and supplier continuity plans. Each threat-to-control mapping helps organisations build layered defenses and agreed cross-stakeholder responses to limit damage and restore services quickly.
- Threat-to-control checklist:
Phishing: MFA, filtering, simulated training, rapid revocation processes.
Data breach: Encryption, least privilege, logging, coordinated disclosure playbooks.
Availability (DDoS): Redundancy, capacity planning, mitigation agreements with providers.
For organisations seeking external support to implement ISO 27032 and maintain continuous assurance, Stratlane Certification offers accredited auditing services and AI-enabled assessment tools that accelerate gap analysis, help prioritise remediation, and support certificate management for related standards. Stratlane blends automated coverage mapping with human auditor validation to scale assessments across large environments while preserving context-sensitive judgement. Request an AI-driven assessment or audit to get an initial gap analysis and a remediation roadmap that integrates with your ISMS and ongoing certificate management. Our partner-led approach helps teams move from guidance to measurable cybersecurity improvements without overloading internal resources.
Frequently Asked Questions
What is the difference between ISO 27032 and other cybersecurity standards?
ISO 27032 focuses on internet security and the collaborative aspects of cybersecurity—how organisations coordinate across networks and stakeholders. Other standards, like ISO 27001, target the information security management system (ISMS). ISO 27032 complements an ISMS by giving practical guidance on cross-organisational incident response, threat sharing and CIIP resilience, making it especially useful in interconnected environments.
How can organizations measure the effectiveness of ISO 27032 implementation?
Measure effectiveness with KPIs such as mean time to detect (MTTD) and mean time to respond (MTTR), plus reductions in incident impact and improvements in coordinated response speed. Track the percentage of critical dependencies covered by resilience plans and use regular audits and assessments to validate alignment with ISO 27032 and reveal where to improve.
What challenges might organizations face when implementing ISO 27032?
Common challenges include change resistance, low awareness of the guidance, and aligning existing processes to new cross-stakeholder workflows. Resource constraints for training and incident coordination can also slow progress. Overcome these by securing executive support, investing in targeted training and using phased implementation with clear, measurable milestones.
How does ISO 27032 address emerging cyber threats?
ISO 27032 promotes a proactive, risk-based approach: continuous monitoring, threat intelligence sharing and incident planning. Its emphasis on layered defenses and cross-stakeholder coordination helps organisations adapt to threats like ransomware, phishing and DDoS and stay ahead of evolving attack techniques.
Can small businesses benefit from ISO 27032 guidelines?
Yes. Small businesses that use internet-facing services or cloud platforms can adopt ISO 27032’s risk-based approach to prioritise protections without overspending. The guidance helps them build essential controls, improve incident response and demonstrate security to customers and partners.
What role does training play in the successful implementation of ISO 27032?
Training is essential. Effective programs ensure employees know detection and response roles, recognise threats and follow escalation procedures. Regular exercises and tabletop scenarios reinforce coordination with partners and suppliers, turning policy into practiced behavior.
How can organizations ensure continuous improvement after implementing ISO 27032?
Maintain a cadence of reviews, audits and assessments that feed lessons learned back into policy and controls. Use threat intelligence and incident post-mortems to refine priorities. Leveraging AI-driven monitoring can surface deviations in near real time and support ongoing adaptation to new threats.
Conclusion
ISO 27032 offers practical guidance to strengthen an organization’s internet security through cross-stakeholder coordination and clearer incident response. Aligning with these recommendations reduces incident impact, streamlines compliance efforts and builds trust with customers and partners. If you’re ready to move from guidance to measurable improvements, explore Stratlane’s AI-driven auditing and certification services to accelerate gap analysis and sustain continuous assurance. Start securing your internet-facing risks today.