ISO 27035 Explained: Best Practices for Incident Management

ISO 27035 — Information Security Incident Management Certification to Strengthen Cyber Resilience
ISO 27035 defines a practical, repeatable approach for managing information security incidents — from preparation and detection through response, recovery, and lessons learned. This guide explains how the standard maps to operational practices, why certification matters for resilience and compliance, and how teams can adopt ISO 27035 alongside an existing ISMS like ISO 27001. You’ll get a clear incident management lifecycle, role-based tasks for Incident Response Teams (IRTs), plus hands-on steps for evidence collection, exercises, and certification readiness. We also describe how AI-assisted auditing speeds evidence analysis and improves audit quality, then walk through a straightforward certification checklist for organizations ready to prove their incident management maturity.
What is ISO 27035? Understanding the Information Security Incident Management Standard
ISO 27035 sets out principles, processes, and best practices for handling security incidents so organizations can limit damage and restore normal operations quickly. The standard provides a repeatable incident lifecycle and assigns roles, tools, and communication channels so teams can detect, report, assess, respond, recover, and learn consistently. Implementing ISO 27035 builds readiness: documented policies, tested playbooks, and trained teams that turn alerts into prioritized actions and measurable recovery outcomes. The sections that follow unpack the standard’s core principles and clarify which incidents and organizations fall within scope.
In practice, implementing ISO 27035 often means building a complete incident management system — a point reinforced by several case studies and research projects.
ISO 27035 Incident Management System Development
This research project develops an incident management system aligned with ISO 27035. Using qualitative methods and BMKG Communication Network Center case studies, the work maps incident management to BMKG’s business processes. Deliverables include policies, documentation, and standardized procedures designed to strengthen BMKG’s ability to manage and mitigate incident threats effectively.
Information security incident management using iso 27035 standard, M Salman, 2023
What are the key principles and objectives of ISO 27035?
ISO 27035 emphasizes five core principles: preparedness, timely detection, structured assessment, decisive response, and continuous improvement. Preparedness means clear policies, defined IRT roles, and runbooks that support fast, consistent action — reducing confusion and speeding containment. Detection and reporting rely on both telemetry and human channels so evidence is captured and triaged against repeatable severity criteria, focusing effort on the highest-impact events. The standard’s improvement loop drives post-incident reviews that refine thresholds, playbooks, and training so each incident improves future outcomes and organizational resilience.
How does ISO 27035 scope apply to organizations?
ISO 27035 is relevant across industries and organization sizes. It provides flexible guidance on incident classification, escalation thresholds, and third-party coordination, making it practical for SMEs, enterprises, and academic institutions alike. The scope covers incidents affecting confidentiality, integrity, or availability — for example, data breaches, ransomware, unauthorized access, and major operational disruptions — while letting organizations tailor classification based on business impact and legal obligations. Cloud and supply-chain scenarios should be explicitly included so third-party incidents and shared-responsibility cases are part of the response plan and contractual reporting rules. Clear scoping helps teams set realistic detection thresholds and decide when an event becomes a formally managed incident.
How does the ISO 27035 Incident Management Process Work? A Step-by-Step Framework
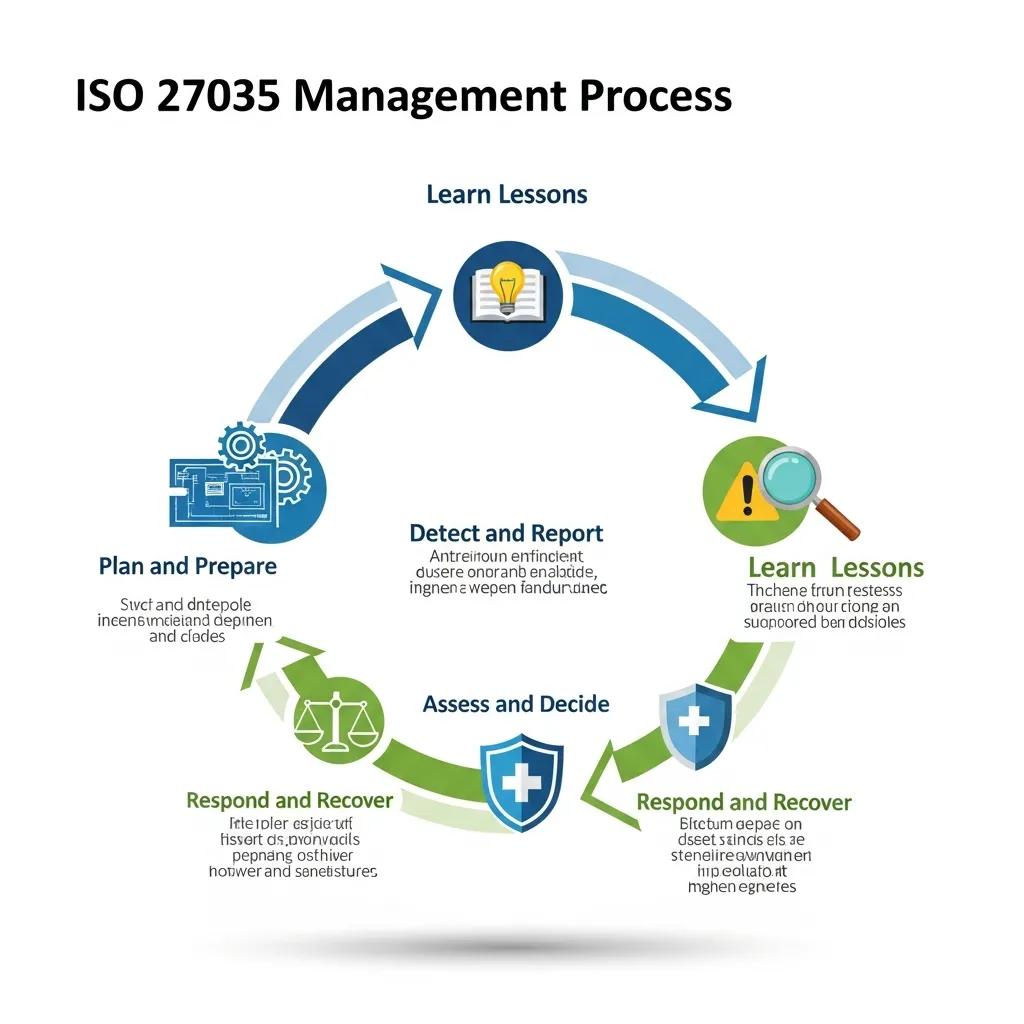
ISO 27035 frames incident management as a lifecycle that turns detection into controlled recovery through defined phases, owners, and deliverables. Following the lifecycle gives teams a repeatable path from readiness to lessons learned and helps improve measurable outcomes like time-to-contain and time-to-recover. Below are the lifecycle phases with concise definitions to make the framework actionable for operational teams.
- Plan and Prepare: Create policies, assign roles, define communications, build playbooks, and provision tooling so the organization is ready to respond.
- Detect and Report: Monitor systems, accept user reports, and collect signals that feed initial triage and evidence capture.
- Assess and Decide: Triage incidents, assign severity, and authorize response actions based on business impact and compliance needs.
- Respond and Recover: Contain the threat, eradicate artifacts, restore systems from validated backups, and keep stakeholders informed.
- Learn Lessons: Run post-incident reviews, track remediation, and update playbooks and training to prevent recurrence.
Recent analyses of ISO 27035:2023 underscore its value as a comprehensive lifecycle framework for incident management.
ISO 27035:2023 Incident Management Framework & Lifecycle
This study proposes a framework for handling security incidents based on ISO/IEC 27035:2023. The 2023 revision offers a full lifecycle approach — from preparation and identification to containment, eradication, and recovery — to address modern incident management challenges.
Recommendations for a Framework for Handling Security Incidents of Electronic-Based Government Systems (SPBE) using the ISO/IEC 27035: 2023 Standard, 2023
This sequence gives teams a practical route from readiness to continuous improvement and clarifies which tools and KPIs map to each phase. The sections below dig into activities, detection methods, response workflows, and learning practices that make these phases operational.
What activities are involved in the Plan and Prepare phase?
Plan and Prepare covers establishing an incident management policy, standing up and training an Incident Response Team, and defining communication and escalation protocols that meet legal and contractual requirements. Core tasks include writing playbooks and runbooks for common incidents, running tabletop exercises to test decision points, and ensuring forensic and logging capabilities preserve chain-of-custody. Tool choices — SIEM, endpoint detection, case management — should align with workflows to enable automated alerts and evidence capture. A readiness checklist helps teams prioritize initial work and resources when starting ISO 27035 implementation.
How are incidents detected, reported, and assessed under ISO 27035?
Detection mixes technical telemetry — logs, SIEM alerts, IDS/IPS signals — with human channels like helpdesks and security hotlines to capture a broad set of signals. Reporting workflows define which channels feed the incident system and how events are logged into a central case platform for triage and auditability. Assessment uses predefined severity criteria that weigh data sensitivity, system criticality, and regulatory impact so the IRT can prioritize containment and escalation. The triage produces a decision record documenting who authorized actions and why, supporting both response and later review.
What are the response and recovery steps in the incident management lifecycle?
Response and recovery follow containment, eradication, and restoration steps with clear ownership and verification to return operations to normal while safeguarding forensic evidence. Containment might mean isolating systems, applying network segmentation, or disabling compromised accounts to stop further damage. Eradication removes malicious artifacts, patches vulnerabilities, and completes forensic analysis to identify root cause. Recovery validates system integrity, restores from clean backups, and runs functional tests before returning services to production. Use communication templates for stakeholder updates and track remediation with KPIs such as Mean Time to Detect (MTTD) and Mean Time to Recover (MTTR) to drive measurable improvement.
How does the Learn Lessons phase improve future incident handling?
Learn Lessons turns incident retrospectives into concrete improvements: run root cause analysis, update playbooks, and schedule targeted training to close gaps found during response. Post-incident reviews should produce a prioritized remediation plan with owners and deadlines and feed into change management so fixes are implemented and verified. Incident metrics — timelines, decision logs, performance against KPIs — inform risk assessments and guide investments in detection tools or staff. Continuous learning completes the lifecycle, enhancing preparedness and aligning team capabilities with evolving threats.
Why is ISO 27035 Certification Important for Businesses? Key Benefits Explained

ISO 27035 certification signals that an organization follows internationally recognized incident management practices — strengthening cyber resilience, simplifying regulatory reporting, and reducing the operational and financial fallout from incidents. Certification confirms that policies, processes, and evidence-handling meet a repeatable standard, giving executives, customers, and regulators confidence that incidents will be managed methodically.
The table below summarizes common business benefits in an Entity | Attribute | Value format to help leaders evaluate the certification investment.
| Benefit Area | Effect | Practical Value |
|---|---|---|
| Regulatory Compliance | Documented, auditable reporting | Faster, clearer notifications and reduced regulatory risk |
| Operational Resilience | Standardized response workflows | Less downtime and consistent recovery procedures |
| Customer Trust | Verifiable incident controls | Competitive edge in procurement and stronger vendor credibility |
How does ISO 27035 enhance cyber resilience and security posture?
ISO 27035 improves resilience by enforcing repeatable detection-to-recovery workflows that shorten detection and recovery times through practiced actions and trained teams. Requiring evidence retention, logging strategies, and playbooks helps organizations contain incidents faster and verify system integrity before restoring services. Exercises and post-incident reviews strengthen cross-functional coordination and ensure detection thresholds and escalation criteria stay aligned with business priorities, reducing exposure to prolonged outages and data loss.
What regulatory compliance and trust advantages does certification provide?
Certification provides tangible evidence that incident management meets a recognized international benchmark, simplifying regulatory reporting under data protection laws and contractual incident obligations. Documented processes and decision logs make it easier to show timely notification, root-cause analysis, and remediation to regulators and affected parties. Commercially, certification reassures customers and partners that the supplier maintains structured incident readiness — a common procurement requirement that can shorten due diligence and improve contracting outcomes.
How does certification minimize the impact and cost of security incidents?
Certification reduces impact and cost by cutting detection and recovery timelines, lowering external investigation fees, and minimizing operational disruption through predefined containment and restoration steps. With playbooks and trained teams, organizations avoid ad hoc decisions that extend downtime and inflate recovery costs. Certification also creates a defensible audit trail that can ease regulatory scrutiny and insurance claims. Faster containment, clearer remediation ownership, and documented improvements help lower both immediate and long-term incident expenses while improving insurability.
What is Stratlane’s AI-Driven Advantage in ISO 27035 Auditing?
AI enhances ISO 27035 audits by automating log correlation, anomaly detection, and evidence prioritization so auditors focus on high-impact controls and context-aware judgments instead of manual data triage. Machine-assisted analysis reconstructs timelines from multiple telemetry sources, surfaces suspicious patterns, and ranks evidence to speed audit work while keeping human oversight for interpretation. The payoff: shorter audit cycles, more consistent findings, and clearer reports that emphasize operational risk and practical remediation. Below we describe how a certification body can embed AI into the audit journey and the service benefits that follow.
Stratlane Certification is an accredited certification body providing ISO 9001, ISO 14001, ISO 27001, and ISO 45001 certifications across the US, EU, and UK. We combine experienced auditors with AI-driven audit tools to improve efficiency and assessment quality, issue certificates in over 27 countries, and support clients from quote through audit scheduling, issuance, and certificate management.
How does AI improve incident detection and analysis during audits?
AI speeds detection and analysis by parsing large volumes of logs, recognizing patterns, and scoring anomalies to reveal event sequences that are hard to assemble manually. Automated correlation connects user activity, system logs, and network telemetry into coherent timelines that help auditors verify whether detection and response matched documented playbooks. Prioritization engines highlight the most relevant evidence, reducing time spent on low-value noise and enabling auditors to concentrate on control effectiveness and root-cause findings. This machine-human pairing raises audit precision while preserving human judgment for nuance.
In what ways does AI streamline the ISO 27035 certification journey?
AI shortens the certification path by accelerating readiness checks, automating evidence collection where allowed, and reducing manual sampling with risk-based selection of controls and incidents for review. During audits, AI-generated summaries and visual timelines help auditors validate compliance faster and produce clearer corrective actions, shortening the overall timeline from quote to certificate. After certification, AI analytics can track remediation trends and flag recurring weaknesses, feeding continuous improvement and improving consistency across distributed environments.
How Does ISO 27035 Complement ISO 27001? Understanding Their Relationship
ISO 27035 adds operational depth to an ISO 27001 ISMS by translating governance-level controls into concrete incident management procedures. ISO 27001 defines the ISMS framework and control objectives; ISO 27035 supplies the incident lifecycle, triage criteria, and playbooks needed to act when incidents occur. The table below maps each standard’s focus and shows where ISO 27035 provides prescriptive operational detail.
| Standard | Focus | Practical Coverage |
|---|---|---|
| ISO 27001 | ISMS governance and controls | Policy, risk assessment, control selection and monitoring |
| ISO 27035 | Incident management lifecycle | Detection, triage, response, recovery, lessons learned |
| Overlap | Incident-related controls | Incident response objectives and evidence requirements |
What are the differences and overlaps between ISO 27035 and ISO 27001?
ISO 27001 and ISO 27035 overlap on incident response controls but differ in purpose: ISO 27001 requires an ISMS and sets control objectives, while ISO 27035 describes the incident lifecycle, triage rules, and operational playbooks. ISO 27001 includes incident management in Annex A (notably A.16) but does not prescribe detailed procedures for detection, forensic preservation, or post-incident reviews — gaps that ISO 27035 fills with actionable guidance. Together they provide governance plus operational execution: policy and risk management from ISO 27001, and incident-specific implementation from ISO 27035.
How can organizations integrate ISO 27035 into their existing ISO 27001 ISMS?
Integrate ISO 27035 by mapping ISO 27001 incident-related controls to ISO 27035 processes, updating ISMS documentation to include playbooks, and embedding incident KPIs in management reviews. Start with a gap analysis to identify missing procedures, evidence rules, and tooling needs, then prioritize quick wins like standardizing reporting channels and training the IRT. Update the Statement of Applicability and control implementation records to reflect ISO 27035 practices, and schedule incident management reviews as part of ISMS audits. These steps turn governance into operational readiness and strengthen both compliance and resilience.
What Are the Steps to Achieve ISO 27035 Certification with Stratlane?
ISO 27035 certification follows predictable stages: preparation, evidence assembly, audit, corrective action, and certificate issuance. Organizations normally scope the certification, perform a readiness assessment, document or update incident policies and playbooks, gather evidence of exercises and responses, and undergo an audit that examines documentation and demonstrated practice. The checklist below outlines a practical sequence to prepare for certification and manage the audit efficiently.
- Conduct a readiness assessment and define the certification scope and boundaries.
- Document incident policies, playbooks, and roles; collect evidence of training and exercises.
- Deploy or verify detection tooling, logging, and evidence-preservation processes.
- Schedule the audit with credentialed auditors, address findings through corrective actions, and complete certificate issuance.
Below we describe Stratlane’s service positioning and how we support clients from quote to certificate management.
Stratlane Certification is an accredited body offering ISO 9001, ISO 14001, ISO 27001, and ISO 45001 certifications across the US, EU, and UK. We use AI-enhanced audit tools to boost efficiency and assessment quality, issue certificates in over 27 countries, employ experienced auditors, and guide clients from initial quote through audit scheduling to certificate issuance and ongoing management.
What are the certification requirements and preparation checklist?
To be ready for certification you need documented incident management policies, playbooks for common incident types, evidence of IRT training and exercises, and technical artifacts such as logging retention and forensic collection procedures. Prepare a prioritized evidence pack — incident logs, exercise reports, post-incident reviews, and change-control records showing remediation of gaps. An internal pre-audit or gap analysis will identify missing artifacts and assign owners to close them before the formal audit, reducing audit effort and speeding corrective-action cycles.
How does the audit and certification process proceed?
The process typically includes a pre-audit readiness review, a remote or on-site audit of documentation and practice, issuance of findings with a corrective action period, and final certification once nonconformities are closed and verified. Auditors assess policy alignment, evidence of detection and response, and effectiveness of post-incident reviews and continuous improvement. Timelines vary by scope; plan for readiness assessment, audit scheduling, and corrective-action cycles. After certification, surveillance and periodic recertification ensure ongoing conformity.
How can businesses get a quote and start their ISO 27035 certification?
To get a quote, provide basic scope details: organizational size, geographic coverage, systems in-scope for incident management, and whether you already have an ISMS such as ISO 27001. A provider will request documentation to estimate audit effort and propose timelines for readiness assessment, audit windows, and corrective-action periods. Clear scoping speeds quoting and scheduling. After certification, effective certificate management helps sustain controls and continuous improvement.
- Prepare Scope Details: List systems, sites, and whether an ISMS exists.
- Gather Evidence: Assemble incident logs, playbooks, and exercise reports for review.
- Request Quote: Share scope and an evidence summary for an accurate estimate and schedule.
This process helps organizations move from readiness to certification with predictable steps and timelines.
Frequently Asked Questions
What types of incidents does ISO 27035 cover?
ISO 27035 covers incidents that affect information confidentiality, integrity, or availability — for example, data breaches, ransomware, unauthorized access, and large operational outages. The standard lets organizations define incident categories and thresholds based on business impact and regulatory obligations so their incident management process remains focused and relevant.
How can organizations measure the effectiveness of their incident management under ISO 27035?
Measure effectiveness with KPIs like Mean Time to Detect (MTTD) and Mean Time to Recover (MTTR), plus metrics on incident frequency, containment success, and remediation closure rates. Regular post-incident reviews, trend analysis, and audits against ISO 27035 help identify weaknesses and track improvement over time.
What role does training play in ISO 27035 compliance?
Training is essential. Regular exercises and role-based training ensure IRT members know their responsibilities and can follow playbooks under pressure. Tabletop exercises and simulations reveal decision gaps and help teams practice coordination and communication, strengthening real-world response capabilities.
How does ISO 27035 integrate with other standards like ISO 27001?
ISO 27035 complements ISO 27001 by supplying operational incident management practices within the ISMS framework. While ISO 27001 covers governance and risk management, ISO 27035 delivers incident detection, response, and learning processes. Organizations typically map ISO 27001 controls to ISO 27035 procedures to create a cohesive security program.
What are the common challenges organizations face when implementing ISO 27035?
Common challenges include resistance to change, limited resources, and gaps in training or tooling. Aligning new incident processes with existing workflows and meeting documentation requirements for certification can also be difficult. Overcoming these challenges requires leadership support, prioritized investments, and a phased approach to implementation.
How often should organizations review and update their incident management policies?
Review policies at least annually or whenever there are major changes — for example, new regulations, significant incidents, or changes in technology or suppliers. Post-incident lessons should feed policy updates promptly. Continuous improvement is a core ISO 27035 principle, so regular review cycles are essential.
Conclusion
Adopting ISO 27035 strengthens an organization’s ability to manage security incidents consistently, reducing operational impact and improving resilience. Certification demonstrates a commitment to repeatable, auditable incident practices that build trust with customers and regulators. If you’re ready to formalize incident readiness, Stratlane can help you prepare, audit, and certify your incident management program — from initial scoping to certificate management.